Security policies are provided in macOS to restrict which apps can run outside of the usual protective system policies. Here’s how macOS Sequoia can override system policies in some cases.
Apple’s macOS is one of the most secure operating systems in the world. Even so, no operating system is foolproof, and security breaches are still possible.
In the past decade, Apple has added several additional security features to macOS which helps improve security. These include but are not limited to:
- Developer ID
- Gatekeeper
- App Notarization
- Digital app signatures
- System Integrity Protection (SIP)
Developer ID and Gatekeeper are two app-related security features that verify and authorize Mac apps in order to allow or disallow them from running. Gatekeeper prevents apps from running unless they are confirmed to come from a registered Apple developer or the Mac App Store.
It’s also possible for Developer ID-only apps to run when downloaded outside the Mac App Store, if they’ve been verified by Apple.
Gatekeeper is what causes the “Verifying” progress window to appear in the Finder the first time you run a newly downloaded app. This window appears as Gatekeeper verifies the signed digital receipts of all of an app’s components on its first run.
In macOS’s System Settings app, you can select whether to allow only Gatekeeper-verified (App Store) apps to run. You can also allow Gatekeeper and apps from registered Apple developers via Developer ID.
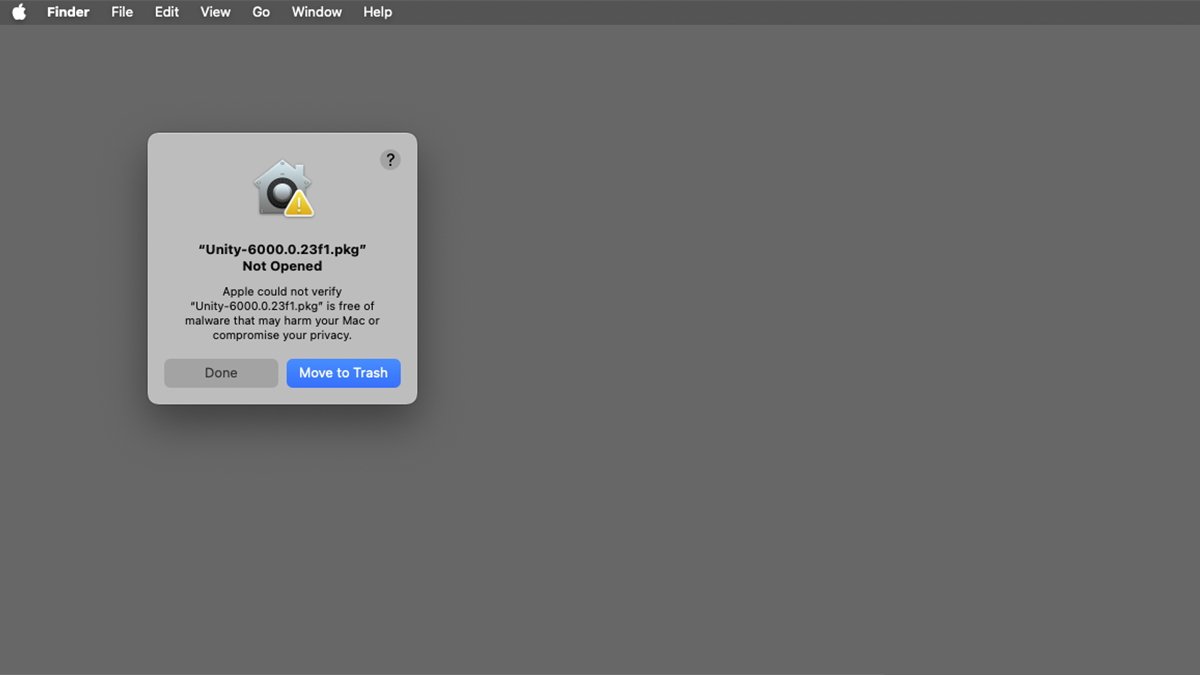
If you try to run a macOS app without either of these security features, you’ll get an alert in the macOS Finder telling you the app can’t be opened. To override this warning, you’ll click Done, then go back to System Settings->Privacy & Security and click the Open Anyway button:
App Notarization adds security to Mac apps and disk images by having Apple verify they don’t contain malicious components.
A digital app signature is an encrypted signing of a Mac app at the time it is built by the developer, and when it is downloaded from the Mac App Store. Digital signatures ensure an app isn’t fake – and that its contents haven’t been tamped with after distribution.
System Integrity Protection (SIP) is a system-wide security feature Apple added to macOS 10.11 El Capitan in 2015. SIP protects critical operating system files from being tampered with, as well as parts of macOS even from the root UNIX user, should it be enabled.
SIP can be disabled and re-enabled in macOS’s Terminal app, but Apple doesn’t recommend doing so since it opens your Mac up to security risks.
Together, these security components are known as Runtime Protection in macOS.
Terminal apps
Apple provides other runtime protections for standalone binary apps, which run the Terminal app. These include extended attributes (xattrs) and other system-level protections.
Some command-line Terminal apps may not be allowed to run with the default system security policies. Apple does this to protect users from unverified malicious third-party command-line Terminal tools.
These restrictions only apply to some apps.
In some cases, ordinary double-clickable macOS apps may need to run separate command-line tools or other software components.
Enabling apps to run other apps
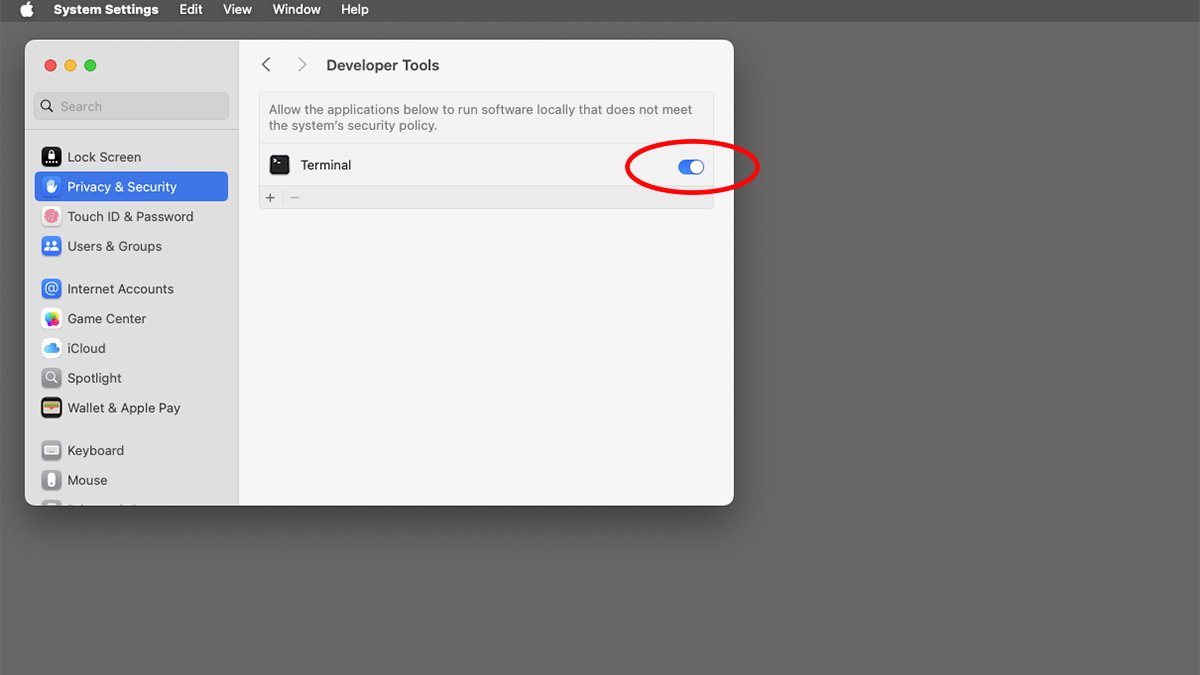
If you want to be able to run an app that needs to run outside of the macOS system security policies in macOS Sequoia, head back to the System Settings->Privacy & Security pane. You need to check each subpage for a switch to enable it.
For example, some command-line developer tools need to run outside system security policies to run other commands, process files, or perform other restricted actions.
In this example, go to System Settings->Privacy & Security->Developer Tools pane and you’ll see the following switch:
Unfortunately in macOS, there’s currently no way to enable this machine-wide, and there probably shouldn’t be since it would subject your Mac to other security risks.
But it is possible to enable this on an app-by-app basis – if an app in question supports it. Again, this feature won’t be available to all apps so you’ll have to check each one individually.
In most cases you won’t need to override macOS security policies, but for some apps in certain cases, you might want to.
For a complete summary of Gatekeeper, Developer ID, and using System Settings for opening apps, see Apple’s Technote 102445, Safely open apps on your Mac.